H. Valters
Ethical Penetration tester / DevSecOps / IT Solution Developer / System administrator
Category Archives: Cyber Security
TeamPass a Self-hosted Password manager to increase organization’s CyberSecurity

In today’s digital age, securing sensitive information within organizations is paramount. With cyber threats becoming increasingly sophisticated, the need for robust password management solutions has never been more critical. TeamPass, a web-based password management system, offers an effective solution to this challenge. This article explores the importance of password security, the benefits of implementing TeamPass…
Kasm New version v1.15 New VPN function and more

In an age where online threats loom large and privacy concerns are at an all-time high, individuals and organizations alike are seeking robust solutions to safeguard their digital activities. Kasm, a cutting-edge platform, emerges as a potent tool to address these pressing concerns. With its multifaceted features, Kasm offers not only protection for businesses and…
How to install Kali Linux in 2023/2024

In this blog post, I will guide you through Kali Linux installation in 2023/2024. It will not be hard. For a YouTube video, that also contains my views on the CyberSecurity and penetration testing industry how I started it all, and how to better start in that industry, you can view it by clicking here…
Kasm Workspace secure way of working and Digital IT Lab
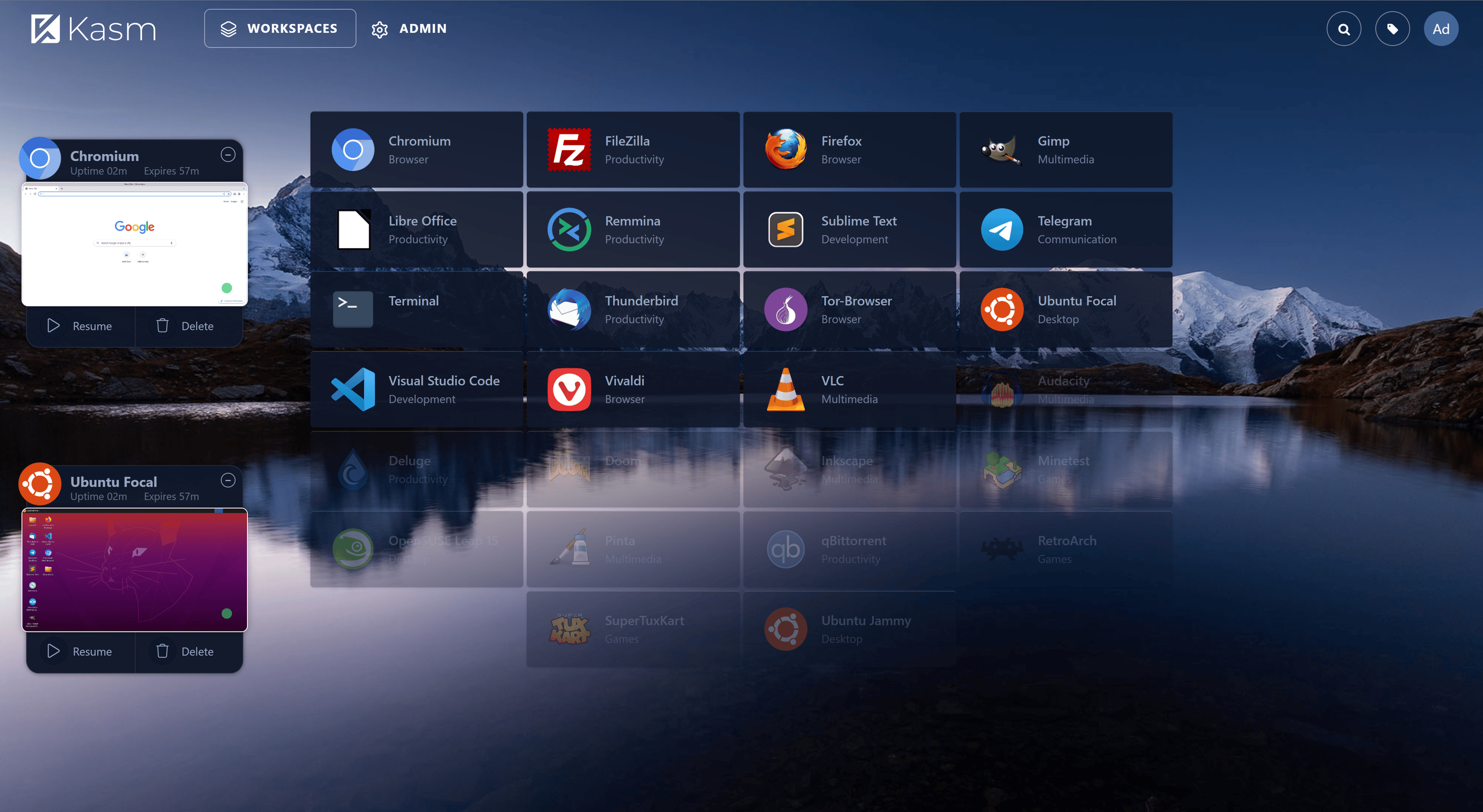
A time ago I wrote an article on how to install and configure Kasm Workspaces. Now some time has passed and there are some changes that I would like to reflect on in this new article. At the same time, I’m also creating a video tutorial on How to install Kasm workspaces. ( The old…
Digital workplace and at the same time your own test lab with Kasm solution

In 2019 COVID-19 shook the world and many companies to continue working started to work remotely. That was a challenging time as I remember that there was a problem to purchase enough laptops large ques to order them and a long wait time, therefore you needed a good communication with the suppliers to get around…
How to Lock down xmlrpc.php in WordPress
This article explains how you can lockdown xmlrpc.php using .htaccess. The WordPress xmlrpc.php endpoint can be misused as an endpoint for brute force attacks. If you do not use xmlrpc.php for any integrations, you might as well disable it completely. Adding these lines to your .htaccess file will disallow access to the endpoint for everyone. Edit your public/.htaccess file and add Note: xmlrpc.php is required by some plugins,…
What is XMLRPC for WordPress and How You Can Stop Hackers From Using It

Website security is a tough thing to solve in the right way. Specifically with security issues related to XML-RPC – as commonly exploited in attacks on WordPress sites. There’s a lot of information available on the internet providing all kinds of solutions, but which are correct? In this article will explain the how, the solutions out there,…
Why Installing a Security Plugin to WordPress Actually Hurt Your Site

WordPress users often lean onto plugins for any required feature or functionality without thinking much about their impact on the site’s performance. There are several WordPress security plugins out there that promise to secure your website from XMLRPC related security issues but in reality, they hurt your site more. Here are some of the reasons…
WordPress Cross-Site Port Attack (XSPA
Cross-site Port Attacks (XSPA) are very common in which the hacker injects the malicious script to retrieve information on TCP ports and IP addresses. In the case of WordPress, XMLRPC is used along with its pingback mechanism to bypass any IP masking such as basic WAF like Cloudflare. In an XSPA attack, the hacker uses pingback….
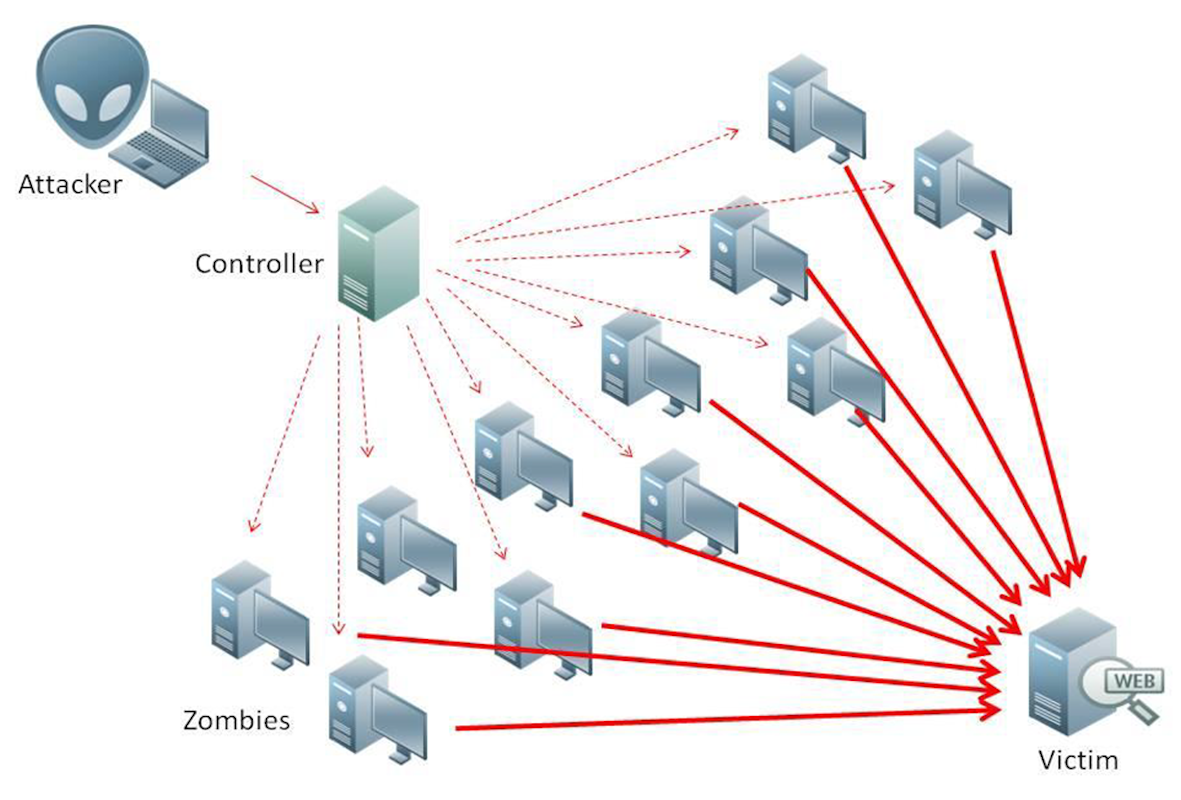
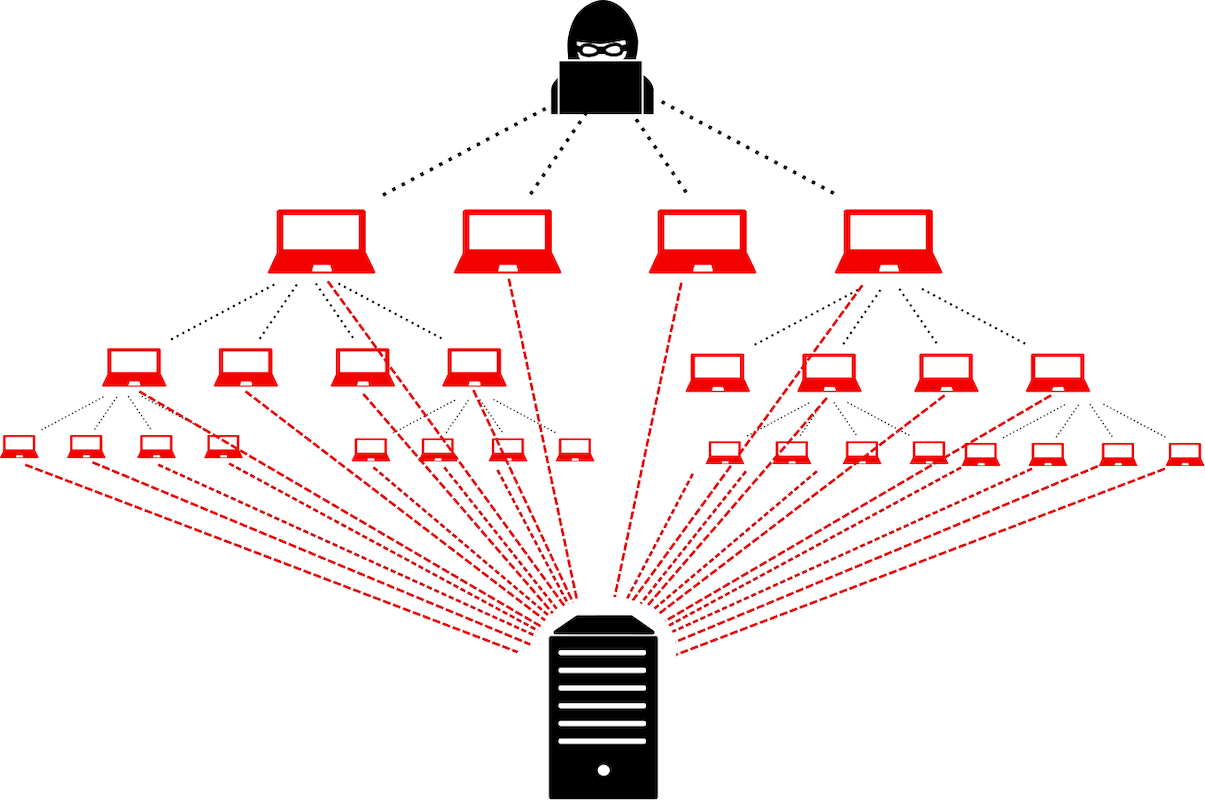
WordPress DDoS Attack

Distributed Denial of Service (DDoS) is one of the most lethal cyber-attacks that can paralyze the server by hitting it with hundreds and thousands of concurrent requests. Hackers use the pingback feature of WordPress along with the xmlrpc.php file to execute such attacks. Ideally, the hacker targets the endpoint or a page that can be…

